Say Goodbye to Manual User Access Reviews
Almost before we knew it, we had left the ground. All their equipment and instruments are alive.Mist enveloped the ship three hours out from port. The spectacle before us was indeed sublime.A red flair silhouetted the jagged edge of a wing.
Reduce your risk and take the misery out of User Access Reviews
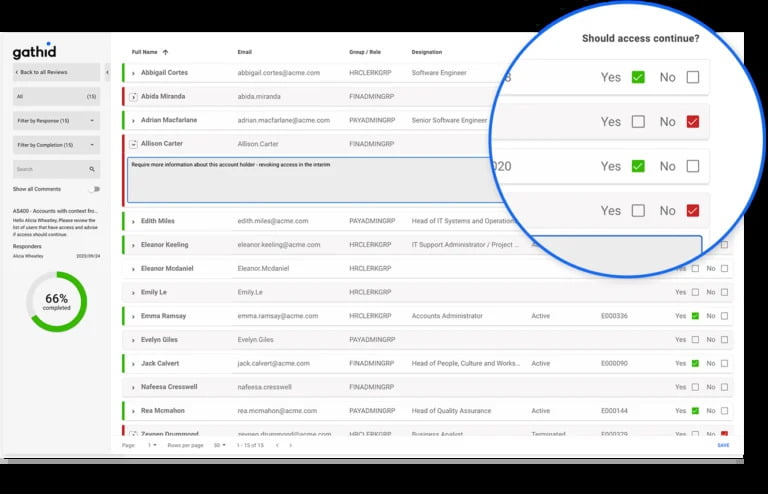
Don’t let time-consuming manual access reviews slow you down and open you to exposure from acesss blind spots!
Automate your user access reviews with Gathid to streamline compliance, improve identity management, and save hundreds of hours. Forget the manual spreadsheets!
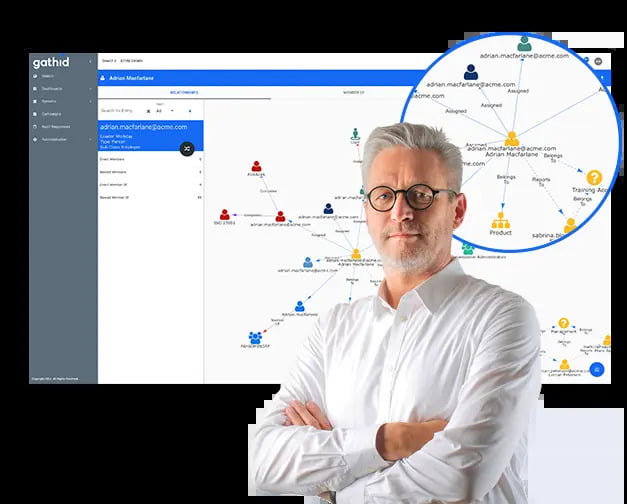
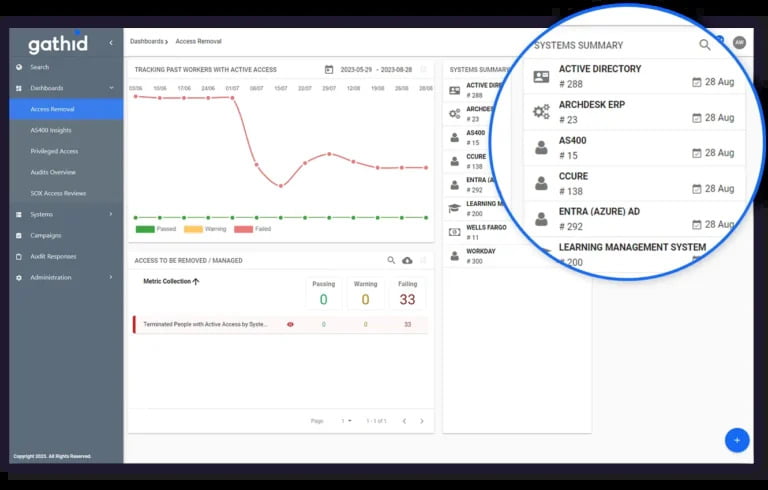
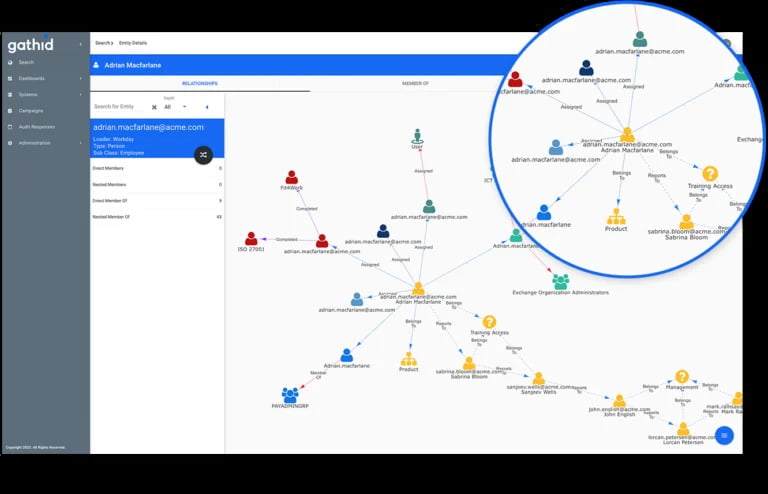
Powered by Gathid’s patented relationship technology, our solution provides real-time visibility into access rights and mitigates security risks across all your systems in a single view.
Gathid maps data collected from each of your connected systems. Their patented technology builds virtual relationships within data, allowing you visibility to each person's access within your organisation (plus external users such as consultants) and relevant contextual information. The time-machine functionality enables a review of historical access rights changes.
Gathid automates user access reviews and delivers up-to-date user and system access information to reduce the pressure during audits and support your compliance programs. With an automatic review process, your teams can quickly close gaps and spend less time on manual review tasks whilst delivering on your compliance targets.